Normally used by organizations for penetration testing, Cobalt Strike is exploited by cybercriminals to launch attacks, says Proofpoint.
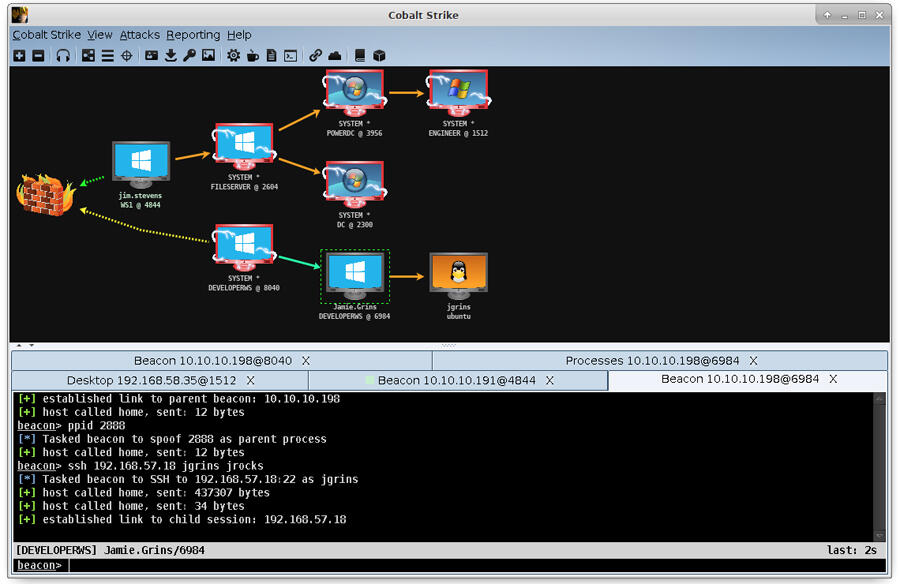
Image: HelpSystems
The same powerful tool used by organizations to enhance their security is being adopted by cybercriminals to help break through their security. Popular penetration testing program Cobalt Strike saw a 161% increase in malicious use from 2019 to 2020 and is considered a high-volume threat for 2021, according to a report released Tuesday by security provider Proofpoint.
SEE: Ransomware: What IT pros need to know (free PDF)
Analyzing the illegitimate use of Cobalt Strike, Proofpoint said it found that the tool is increasingly being used by attackers as an initial access payload, meaning it's enlisted to deploy the initial malicious payload onto victimized machines. This is a change from past instances when Cobalt Strike was used more as a second-stage tool that played a role once the targeted systems had already been accessed.
Cobalt Strike first surfaced in 2012 as a tool to help organizations detect gaps in their security defenses. The program works by emulating an actual attack from advanced threat actors, showing users exactly where their defenses are weak and in need of improvement. In 2015, Cobalt Strike 3.0 hit the market as a standalone adversary emulation program. A short time later in 2016, Proofpoint had already started seeing cybercriminals using the tool for their own malicious purposes.
Cybercriminals are able to grab Cobalt Strike through different resources. They can buy it directly from the vendor, though that requires verification. They can snag a version on the Dark Web through different hacker forums. They can even find illegitimate versions of the program. In March 2020, a cracked version Cobalt Strike 4.0 became available to attackers, according to Proofpoint.
In the past, the use of Cobalt Strike in cyberattacks was largely confined to well-funded cybercriminal groups and advanced persistent threat (APT) groups. From 2016 through 2018, around 66% of the Cobalt Strike campaigns witnessed were attributed to these types of groups. But between 2019 and 2021, that percentage plummeted to just 15%, indicating that Cobalt Strike is now being used by more commonplace attackers.
"Our data shows that Cobalt Strike is currently used by more cybercrime and general commodity malware operators than APT and espionage threat actors," said Sherrod DeGrippo, Proofpoint's senior director of threat research and detection. "This means it has gone fully mainstream in the crimeware world. Financially motivated threat actors are now armed similarly to those financed and backed by various governments."
Still, the tool's use in cyberattacks remains a popular strategy among major cybercrime groups.
One group cited by Proofpoint is A800, which tries to deploy banking malware or malware loaders. In the past, this group downloaded a backdoor exploit called BazaLoader, which then downloaded Cobalt Strike. But in February 2021, A800 started using Cobalt Strike as a first-stage payload sent via malicious URLs.
Another group observed using Cobalt Strike is TA547. Since the middle of 2021, this group has been using malicious Microsoft Office attachments to deploy malware. In February 2021, TA547 starting exploiting Cobalt Strike as a second-stage payload for command and control communications.
A third group that likes to use Cobalt Strike is TA415, which Proofpoint said is believed to be associated with the People's Republic of China. This group was found using Cobalt Strike as a first-stage payload in the middle of 2020. Last September, the U.S. Department of Justice indicted several members of this group, describing their use of Cobalt Strike in the indictment.
In one series of campaigns, TA415 used the tool to attack organizations in the airline industry. The group may have even used Cobalt Strike in a supply chain attack against SITA, an IT provider for several airlines around the world.
"Offensive security tools are not inherently evil, but it is worth examining how illegitimate use of the frameworks has proliferated among APT actors and cybercriminals alike," said DeGrippo. "The use of publicly available tooling aligns with a broader trend observed by Proofpoint: Threat actors are using as many legitimate tools as possible, including executing Windows processes like PowerShell and WMI; injecting malicious code into legitimate binaries; and frequently using allowable services like Dropbox, Google Drive, SendGrid, and Constant Contact to host and distribute malware."
Looking ahead, Proofpoint said it expects Cobalt Strike will continue to be used in cyberattacks. Already, tens of thousands of organizations have been hit with Cobalt Strike campaigns, a number Proofpoint anticipates will rise this year.

Cybersecurity Insider Newsletter
Strengthen your organization's IT security defenses by keeping abreast of the latest cybersecurity news, solutions, and best practices. Delivered Tuesdays and Thursdays
Sign up todayAlso see
- How to become a cybersecurity pro: A cheat sheet (TechRepublic)
- Social engineering: A cheat sheet for business professionals (free PDF) (TechRepublic)
- Shadow IT policy (TechRepublic Premium)
- Online security 101: Tips for protecting your privacy from hackers and spies (ZDNet)
- All the VPN terms you need to know (CNET)
- Cybersecurity and cyberwar: More must-read coverage (TechRepublic on Flipboard)



:strip_exif(true):strip_icc(true):no_upscale(true):quality(65)/cloudfront-us-east-1.images.arcpublishing.com/gmg/MGOPKQZ2QJC5ZBIZIJ45OJE3VE.jpg)


:strip_exif(true):strip_icc(true):no_upscale(true):quality(65)/cloudfront-us-east-1.images.arcpublishing.com/gmg/ZNDEDHWC3NDWJL7JPG25667QLY.jpg)
 English (US) ·
English (US) ·