Your Linux server libraries might be out of date, leading to security issues. CloudLinux has a tool that can quickly list those out-of-date libraries on AlamaLinux or a similar distribution.

Image: iStockphoto
CloudLinux has burst onto the scene as a major player in the Linux server game. This started with their release of AlmaLinux, to take the place of CentOS Stream. That was followed up with the addition of a Linux support service, called TuxCare. The company has continued its show of support by offering a tool that should give Linux server admins some much-needed oxygen. Said tool is UChecker, which can scan your RHEL-based servers for outdated libraries, but in-memory and on disk. This is an important task, one that poses a significant challenge otherwise.
UChecker can scan the likes of RHEL, CentOS (but not CentOS Stream), AlmaLinux, Rocky Linux and CloudLinux Solo. In fact, just about any server distribution based on RHEL can be scanned with UChecker. I've attempted to use it on Ubuntu-based distributions and even Fedora, with no luck—stick with the likes of AlmaLinux and Rocky Linux and you'll be good to go.
Let me show you how easy UChecker is to use.
SEE: Kubernetes: A cheat sheet (free PDF) (TechRepublic)
What you'll need
- A supported server distribution
- A user with sudo privileges
How to install dependencies
UChecker depends on Python, so before you can run the command, you must make sure to install it with the command:
sudo dnf install python3 -yOnce this dependency is met, you're ready to run the UChecker tool.
How to use UChecker
There are two ways you can use UChecker: with or without curl. If you'd prefer to have the tool on hand, without having to download it every time, you'll want to download the script and save it to the local drive. That's my preferred method because I might forget the URL of the script and have to take the time to find it. With the script saved to the local drive, I only have to run it via Python.
With that in mind, download the script with the command:
wget https://kernelcare.com/ucheckerOnce the script is saved to the local drive, run it with the command:
sudo LOGLEVEL=debug python3 ucheckerUChecker will dive in and start running checks against your installed libraries. If it finds anything out of date, it'll report back to you (Figure A).
Figure A
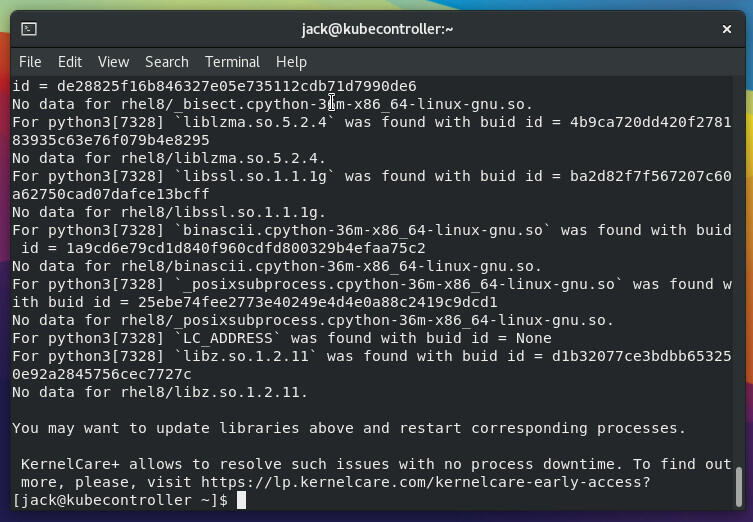
An out-of-date installation of AlmaLinux has several out-of-date libraries.
The one caveat to using the above method is that CloudLinux might make updates to the script. If you always want to be running the latest version, you could use the curl method, like so:
curl -s -L https://kernelcare.com/uchecker | sudo LOGLEVEL=debug pythonOne way of resolving the found issues is to subscribe to KernelCare+, which will work to automatically patch those out-of-date libraries. If you don't want to go the KernelCare+ route, you'll have to upgrade those libraries manually, which can be a challenge. However, in my case, I ran standard sudo dnf update -y, followed by a reboot, which did take care of the issue. I re-ran UChecker and there were no issues found.
You might have installed some libraries via a method other than your package manager, such as from source. That being the case, should you find the full upgrade doesn't take care of what is reported, you might then have to go through each line of the UChecker output and address the update for each library, one at a time. This can be tedious, but if you want to ensure your servers are at their most secure, this is a task you'll need to take on.
Subscribe to TechRepublic's How To Make Tech Work on YouTube for all the latest tech advice for business pros from Jack Wallen.

Data Center Trends Newsletter
DevOps, virtualization, the hybrid cloud, storage, and operational efficiency are just some of the data center topics we'll highlight. Delivered Mondays and Wednesdays
Sign up todayAlso see
How to easily join an AlmaLinux server to an Active Directory Domain with Cockpit (TechRepublic)
How to become a developer: A cheat sheet (TechRepublic)
Kubernetes: A cheat sheet (free PDF) (TechRepublic)
Could Microsoft be en route to dumping Windows in favor of Linux? (TechRepublic)
A guide to The Open Source Index and GitHub projects checklist (TechRepublic Premium)
How open source-software transformed the business world (ZDNet)
Linux, Android, and more open source tech coverage (TechRepublic on Flipboard)



:strip_exif(true):strip_icc(true):no_upscale(true):quality(65)/cloudfront-us-east-1.images.arcpublishing.com/gmg/MGOPKQZ2QJC5ZBIZIJ45OJE3VE.jpg)


:strip_exif(true):strip_icc(true):no_upscale(true):quality(65)/cloudfront-us-east-1.images.arcpublishing.com/gmg/ZNDEDHWC3NDWJL7JPG25667QLY.jpg)
 English (US) ·
English (US) ·